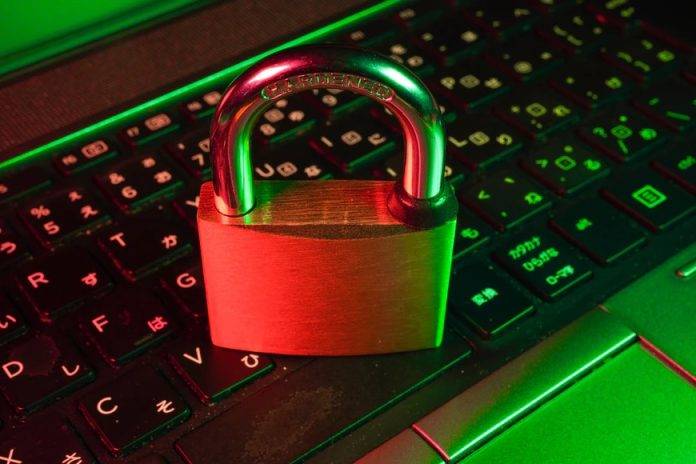
There are multiple reasons why a person can become a victim of a cybercrime. However, not all of them are directly related to the use of technology. There are certain elements associated with their behavior, such as unconscious biases, that contribute to increasing their vulnerability to this type of attack. We will tell you what they are, so you can identify them and know how to protect yourself.
If you are thinking that cyber attacks can only happen to businesses, you are wrong! You can be the next victim. Because the current context derived from the COVID-19 crisis has caused an acceleration of digitization in society and many areas of people’s lives have begun to develop more frequently in the digital environment.
This increased activity on the internet has inevitably meant that their exposure to possible digital attacks has also grown. For this reason, it is more necessary than ever to be vigilant and use all possible resources to try to avoid becoming a target of cybercriminals.
Even though some practices and tips, such as having secure passwords, help prevent internet risks, it is also important to know that there are elements associated with the behavior of people that directly affect the increase in their vulnerability to cyber attacks and that knowing them can help to achieve greater protection.
Factors that increase our vulnerability:
There are extrinsic and intrinsic variables to people that are related to their degree of vulnerability when they become victims of a cyber attack.
First, there are extrinsic variables, which are completely foreign to the person and, as their name suggests, cannot be controlled. These are, on the one hand, the attractiveness of the victim, that is, if they have any assets (for example, of a financial, reputational, or informational nature) that may be of interest to cybercriminals.
And on the other hand, the impact and cost that the attack implies for the criminal – that will be something that determines his attractiveness as well.
Then, there are also intrinsic variables, which are related to the person and can be controlled. They are the following:
– Knowledge: It is clear that having technical skills has an impact on personal security and that the more knowledge the victim has about cybersecurity, the more elaborate and conscientious his behavior will be. However, it is important to note that knowledge alone does not make you immune to cyberattacks.
– The context: There are multiple contextual elements, such as stress, fatigue, or boredom, that undermine the ability to pay attention to the elements that appear in the digital environment. A good example is the time of confinement, in which most people have had to deal with feelings and situations that they were not used to and, most likely, have paid less attention to possible risks.
– Unconscious biases: Another factor that we can try to control and that influences our vulnerability is the existence of cognitive biases: mental schemes or ways of processing reality.
As the experts indicate, the most frequent biases behind increased vulnerability are:
– Delegated responsibility: It occurs when people tend to think that protection does not depend on oneself and, therefore, being careful is delegated to others. For example, when someone buys a computer from a good brand, they might think that they are already protected against everything, and therefore, they relax and don’t worry.
– Overconfidence when perceiving risks: Many times, the probability of an attack happening is not sufficiently valued. An example can be when you enter a web page with an insecure URL and think that nothing will happen because you are there only for a short time. The negative consequences of risky behavior are underestimated.
– The easiest will always win: It is a common thought in people, who tend to minimize effort. A good example is when you have the same password for multiple websites because having different ones is hard to remember.
– Follow social norms: It is also common. For example, it is common to share personal passwords with friends and family for the sake of showing trust. Or disclosing too many personal details on social media just to be relatable or open.
– Continuous connection: Being permanently connected has made people much more dependent, especially in the current world.
– Overexposure to the stimuli of the digital environment: Exposure to content, such as pop-up windows with advertising, is very high and makes people, who are used to it, accept it without paying attention.
In addition to these intrinsic variables, there are demographic characteristics, such as gender, age, or belonging to certain cultural groups, which can also sometimes contribute to some extent to making people more vulnerable to cyber attacks.
Do everything you can to protect yourself:
It has become clear that cybercriminals have a great deal of knowledge about people’s behavior and their psychological needs for affection and recognition, and that they use these in their attacks to generate effective hooks to lure people into their trap. For this reason, it is especially important to highlight these vulnerabilities and be aware that they exist to be especially careful with them.
Important cybersecurity recommendations:
– Research and learn on your own. Then spread the knowledge and educate people around you.
– Get advice from cybersecurity experts. There are a lot of online magazines and social media channels that cover the topic of cyber security.
– Take care of your computers and other devices and use quality antivirus. Don’t neglect this point, it is better to pay some money and be well-protected. The most popular antivirus software these days is Bitdefender, Norton and McAfee.
– Keep all programs up to date.
– Use strong passwords. Never use the same passcode for several platforms. Don’t include any personal details or favorite words – those make it easier for hackers to crack your password. In case remembering all the passcodes is hard, use a password manager.
– Before starting to communicate with an unknown person, you can use a tool like Nuwber. By using this website, you can make sure that an unknown person is genuine and honest about themselves.
– In the case of companies, implement a training plan for workers. Educate your employees on the types of cyber attacks, how to recognize and prevent them.
– Determine the sensitivity of the stored information on all your devices and act accordingly. If possible, use encryption on sensitive and important files.
– Follow the security protocols developed by experts.
– Perform technical cybersecurity analyses periodically. Regularly scan your devices with your antivirus software.
Despite the fact that everyone on the internet is exposed and is a potential victim of a cyberattack, it is essential to continue fighting against these cybercriminals and do everything possible to make it difficult for them to hack you.
To continue protecting yourself and avoiding all possible risks, you can follow the above-mentioned recommendations.